
Security Is Architecture, Not a Feature
Encryption, access control, and data sovereignty embedded in every layer of the platform. Every customer gets the same security posture.
Encryption
All data encrypted at rest and in transit using FIPS 140-3 validated cryptographic modules — from the OS through containers and storage.
Powered by the FIPS 140-3 validated OpenSSL module on Ubuntu 24.04 LTS across all infrastructure layers (CMVP Certificate #5115).
Data at Rest
- Block Storage — Ceph-backed encryption at the storage layer
- Secrets — AES-256 with dedicated Key Encryption Key
- Object Storage — Server-side encryption for S3 buckets
- Backups — Inherit encryption from source resources
Data in Transit
- TLS 1.2+ — All API endpoints and dashboard connections
- HAProxy Gateway — Modern cipher suites at TLS termination
- Internal Encryption — Service-to-service communication encrypted
- Console Sessions — noVNC encrypted end-to-end
Key Management
- AES-256 — Platform-managed Key Encryption Key
- Server-Side Generation — Keys never transit to your browser
- Multiple Types — Symmetric, asymmetric, certificates, passphrases
- Auto-Hide — Revealed payloads hide after 30 seconds
Identity & Access Control
Enterprise authentication with SSO federation and granular role-based access.
Authentication
- Single Sign-On — SAML 2.0, OIDC, and LDAP/AD federation
- Multi-Factor Authentication — TOTP or WebAuthn enforcement
- PKCE Flow — No passwords stored by the dashboard
- Session Management — Configurable timeouts with real-time revocation
Authorization
- Six RBAC Roles — Org Admin, Project Admin, Member, Reader, Security, Auditor
- API-Level Enforcement — Not just UI restrictions, unauthorized API calls return 403
- Project Isolation — Resources invisible across project boundaries
- Credential Management — API tokens, EC2 keys, SSH keys with rotation support
| Role | Scope | Access Level |
|---|---|---|
| Org Admin | Organization | All projects, users, billing, settings |
| Project Admin | Project | Full access within one project |
| Member | Project | Create and manage resources |
| Reader | Project | View-only access |
| Security | Project | Firewalls and secrets only |
| Auditor | Organization | Read-only everywhere, audit logs |
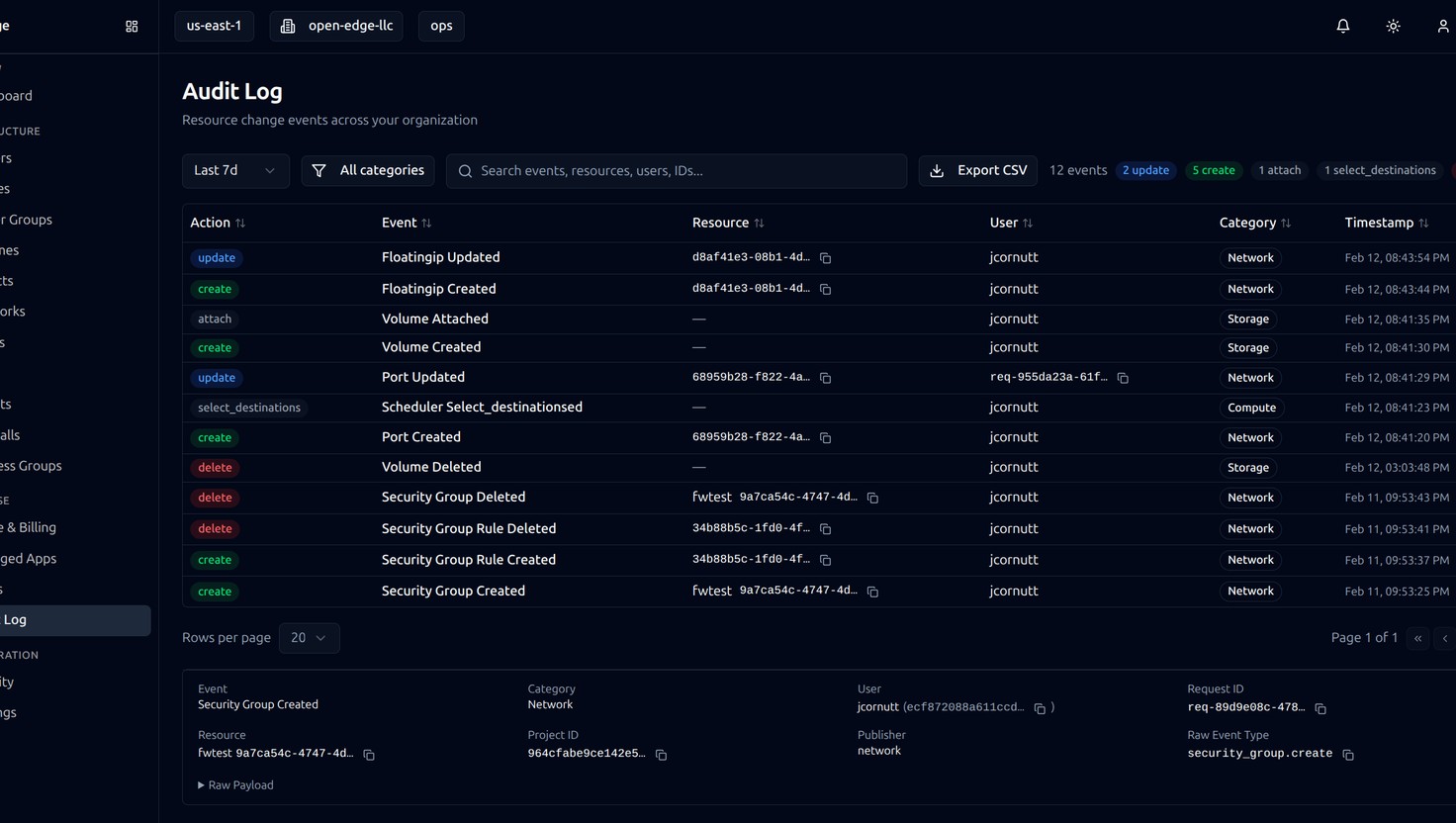
Full Audit Trail
Every resource change is logged with action type, user, resource ID, category, and timestamp. Filter, search, and export your full audit history.
Network Security
Tenant isolation and enterprise-grade firewall management.

Tenant Isolation
- Virtual Networks — Isolated per tenant with no cross-tenant visibility
- OVN SDN — Distributed virtual routing with hardware-accelerated datapath
- Port Security — Anti-spoofing prevents MAC and IP impersonation
Firewall Management
- Ingress & Egress Rules — Protocol, port, and source/destination control
- Traffic Simulator — Validate policy before deployment
- Effective Rules View — Merged policy across all attached groups
- Shadowed Rule Detection — Identify ineffective rules
- Permissive Rule Warnings — Flag rules open to 0.0.0.0/0
Ready to see how Open Edge fits your infrastructure needs?
Data Sovereignty
US jurisdiction. Contractual guarantees. Full transparency.
- US-Only Infrastructure — All resources physically in US data centers
- US-Person Access — Managed by US-based personnel
- No Foreign Replication — Data never leaves US jurisdiction
- Contractual Residency Guarantees — Included in every agreement
Regulatory-Ready Architecture
Our infrastructure is designed to support workloads subject to regulatory requirements, including:
- ITAR — US-person access and US-soil data residency
- CMMC — Security controls for defense contractor workloads
- State Privacy Laws — CCPA/CPRA, VCDPA, and other state-level requirements
- HIPAA — Architecture supports HIPAA-eligible workloads
- SOX — Audit trail and access control capabilities

Infrastructure Security
Physical, platform, and operational security at every layer.
Physical Security
Open Edge infrastructure is deployed in enterprise-grade US data centers: Iron Mountain VA-1 (Manassas, VA) and STACK Infrastructure POR02A (Hillsboro, OR — coming Q2 2026).
- 24/7 on-site security and surveillance
- Biometric access controls
- Redundant power (N+1 UPS + generators)
- Redundant cooling systems
- Fire detection and suppression
- Multiple network uplinks with BGP peering
Platform Architecture
- Ubuntu 24.04 LTS with FIPS 140-3 validated OpenSSL on all nodes
- Multi-node control plane with automatic failover
- HAProxy gateway with TLS and health checks
- Ceph replicated storage with encryption across nodes
- Kolla-Ansible automated, auditable deployment
Monitoring & Response
- Prometheus continuous metrics collection
- Configurable threshold-based alerting
- Alert lifecycle with full audit history
- 24/7 proactive operations team
Shared Responsibility
Clear boundaries between what we manage and what you manage.
| Responsibility | Open Edge | Customer |
|---|---|---|
| Physical data center security | Ours | — |
| Network infrastructure | Ours | — |
| Hypervisor and control plane | Ours | — |
| Platform updates and maintenance | Ours | — |
| Encryption at rest and in transit | Ours | — |
| Monitoring and alerting | Ours | — |
| Incident communication | Ours | — |
| Firewall rule configuration | — | Yours |
| Application security | — | Yours |
| Data classification | — | Yours |
| User access management | Shared | Shared |
| Compliance documentation | Shared | Shared |
| Backup verification | Shared | Shared |
Want to see the full platform in action?
Security Practices
How we operate, and where we are in our compliance journey.
Open Edge follows SOC 2 and ISO 27001 control frameworks across our operations — including access management, change control, incident response, encryption, and monitoring. All cryptographic operations use FIPS 140-3 validated modules. While we have not yet undergone formal third-party certification audits, our platform is built and operated according to these standards.
We maintain transparency about where we are in our compliance journey. If your organization has specific certification requirements or timelines, contact us to discuss your needs.
Questions About Our Security Practices?
Our team is available to discuss your security and compliance requirements in detail. We are happy to answer security questionnaires and walk through our controls with your team.